Takeways
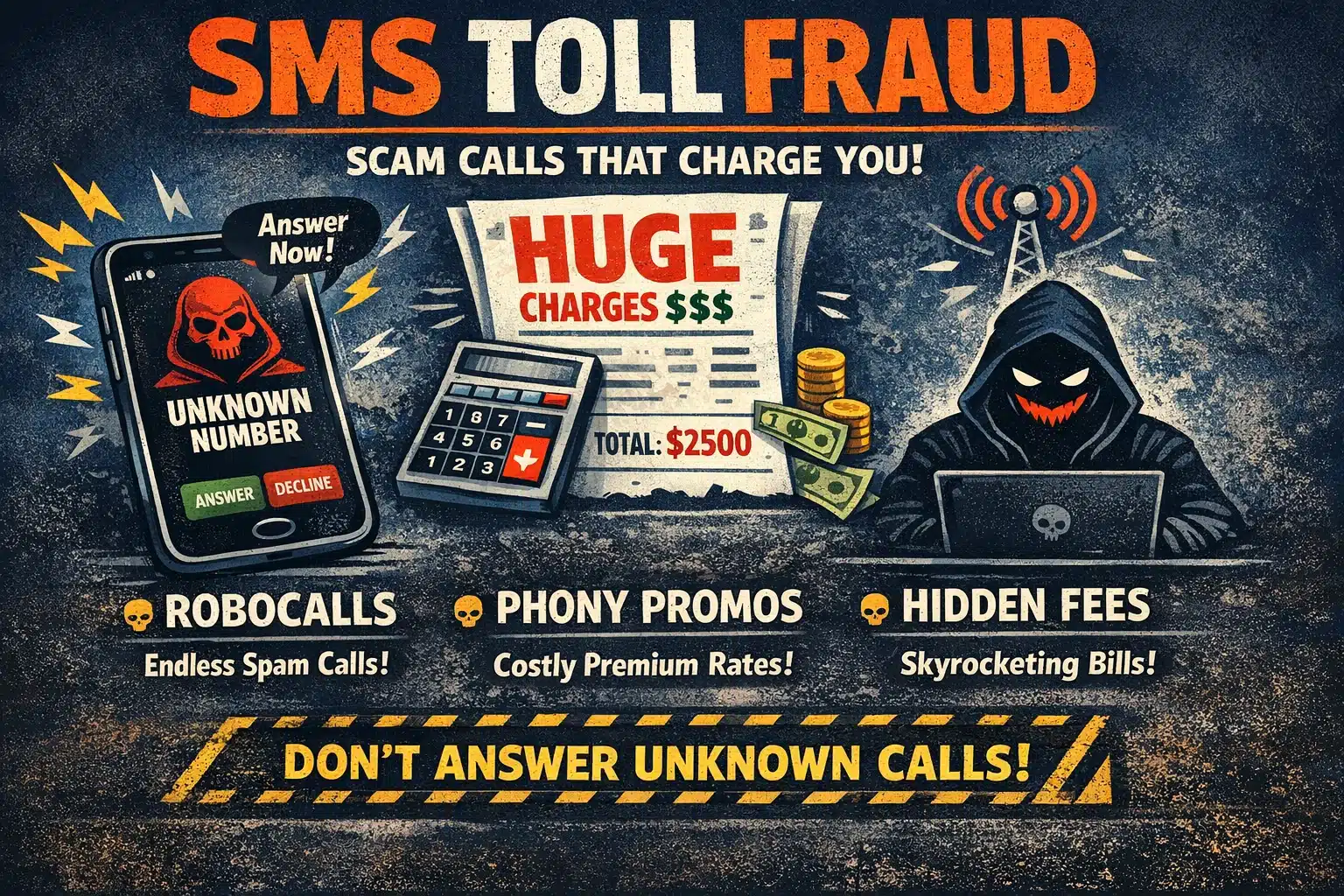
1. What is SMS Toll Fraud?
SMS Toll Fraud, also known as SMS Pumping or Artificially Inflated Traffic (AIT), occurs when fraudsters use bots to trigger massive amounts of SMS messages to high-cost or premium-rate numbers to profit from the resulting termination fees.
2. How has SMS Toll Fraud evolved in 2026?
Attackers now use “Flash Attacks” to drain budgets in minutes and leverage generative AI to mimic human behavior, allowing them to bypass traditional rate limits and simple security filters.
3. Why is IP-based rate limiting no longer enough?
Modern botnets use residential proxies to hide behind millions of legitimate home IP addresses. Because each request looks like it comes from a unique, real user, IP-based blacklists fail to detect the attack.
4. How does Device Fingerprinting help stop SMS Fraud?
Device fingerprinting identifies a user’s unique hardware and browser signature rather than just their IP address. This allows the system to recognize when a single device is attempting to trigger thousands of OTPs, even if the attacker is rotating through thousands of different residential proxy IPs.
5. What is the role of Behavioral Analytics in preventing SMS Fraud?
Behavioral analytics track how a user interacts with a page—such as mouse movement acceleration and typing speed. Since bots often exhibit “perfect” or rhythmic patterns, this layer can stop a fraud attempt before the user even clicks the “Send SMS” button.
Introduction
SMS (Short Message Service) remains a cornerstone of global commerce in 2026. From Two-Factor Authentication (2FA) to shipping notifications, businesses rely on mobile messaging to bridge the gap between digital services and physical users.
However, this reliance has birthed a sophisticated shadow industry. SMS Toll Fraud, also known as SMS Pumping or Artificially Inflated Traffic (AIT), has evolved from a technical nuisance into a multi-billion-dollar threat. According to research by Juniper Research, the total cost of messaging fraud in 2025 is projected to reach $80.5 billion. In 2026, organized syndicates leverage generative AI and distributed botnets to bleed corporate budgets dry.
This guide explores the evolution of the threat and provides a roadmap for implementing a future-proof SMS Toll Fraud Protection strategy.
The State of SMS Security in 2026
The threat landscape has shifted significantly. Market intelligence from the Identity Theft Resource Center indicates that fraudulent traffic now accounts for nearly a quarter of global A2P volume in specific high-risk corridors.
The “Flash Attack” Phenomenon
In 2026, SMS Toll Fraud is no longer a slow-burn process. Attackers now execute Flash Attacks. Using high-speed cloud infrastructure, fraudsters trigger hundreds of thousands of SMS requests within a 10-minute window. By the time an automated billing alert reaches a DevOps team, the company has often already incurred tens of thousands of dollars in transit costs.
Generative AI and Human-Mimicry
The primary differentiator in 2026 is the role of AI. Attackers use Large Language Models to mimic human behavior on registration forms. As noted in Gartner’s security forecasts, the proliferation of AI-driven automation has made identifying a bot vs. a user nearly impossible for legacy firewalls that rely on simple pattern recognition.
Why Legacy Security Fails Against Modern Threats
Many businesses still rely on simple Rate Limiting or IP-based blacklisting. In the current environment, these methods are insufficient for several reasons:
Many businesses still rely on simple rate limiting or IP-based blacklisting as their primary line of defense. In the current 2026 environment, these methods are insufficient due to the fundamental shift in how attackers bypass traditional filters:
1. Industrial-Scale Residential Proxy Networks
Modern botnets no longer originate from suspicious data centers or known VPN ranges. Instead, they route traffic through millions of legitimate home internet connections. This ensures every request appears as a standard household user, rendering IP-based reputation scores and basic geofencing ineffective.
When an SMS Toll Fraud attack is distributed across 50,000 unique residential IPs, traditional threshold-based blocking fails to trigger until the financial damage is already irreversible.
2. Exploitation of Valid but “Trashed” Numbers
Fraudsters have moved beyond using invalid or unassigned numbers. Research from the AB Handshake Community indicates that a staggering 75% of fraudulent SMS attempts now involve valid numbers that are simply trashed within the delivery chain.
Attackers cycle through these verified SIM cards and hijacked ranges at millisecond speeds. Because these numbers are technically legitimate, standard number intelligence services often flag them as safe, allowing the fraud to bypass initial pre-send checks.
3. Systemic Carrier Complicity and Revenue Sharing
The persistent issue of carrier complicity creates a unique economic challenge for SMS Toll Fraud Protection.
The profit participation loop between rogue Tier-4 carriers and fraudsters remains a primary driver of SMS Toll Fraud. These carriers profit from the termination fees of inflated traffic, a trend detailed in the MEF Trust in Enterprise Messaging Report. This systemic alignment of interests means that enterprises cannot rely on the telecom supply chain to self-regulate; protection must be implemented at the application layer where the request is first generated.
Core Framework for SMS Toll Fraud Protection
To effectively stop SMS fraud in 2026, companies must move away from reactive monitoring and adopt a Zero-Trust communication model. This framework is built upon three technical pillars designed to intercept artificial traffic before it ever reaches the service provider’s gateway.
1. Device Fingerprinting and Hardware Attribution
In an era where IP addresses are easily rotated via residential proxies, the most reliable way to identify botnets is through persistent device fingerprinting.
By capturing unique hardware attributes, browser configurations, and canvas rendering signatures, businesses can create a unique “ID” for every user agent. This level of SMS Toll Fraud Protection allows security systems to recognize when a single device is attempting to trigger hundreds of OTPs, even if it is switching IPs between every request. Unlike cookies, hardware-based fingerprints are difficult to spoof, making them a cornerstone for identifying organized “Flash Attacks” in 2026.
2. Real-Time Behavioral Analytics
2026-grade defense focuses on how a user interacts with a page rather than just what they submit.
Real-time behavioral analytics track micro-interactions such as keystroke dynamics, mouse hover patterns, and the time elapsed between page load and the SMS request. Automated scripts, even those powered by generative AI, often exhibit rhythmic or “inhumanly perfect” interaction patterns. By analyzing these nuances, systems can flag a session as “suspicious” if the signup process happens too quickly or follows a predictable, non-human trajectory. This proactive layer ensures that the SMS trigger is never activated for sessions exhibiting bot-like characteristics.
3. Granular Geofencing and Prefix Control
Geographic control remains a highly effective component of SMS Toll Fraud Protection. By implementing a “Permit-by-Exception” policy, businesses can drastically reduce their attack surface through specific logic hooks. This involves automatically blocking or requiring extra verification for SMS sent to premium-rate international prefixes or known high-cost corridors.
For example, if your business logic identifies a user registering with a Western European IP but providing a phone number from a high-risk Pacific island prefix, the system can automatically divert that user to a high-friction secondary check or an alternative verification method like Email or WhatsApp.
Advanced Toolset Against SMS Fraud for 2026
To implement a robust SMS Toll Fraud Protection strategy, enterprises must leverage a combination of behavioral, network, and intelligence-based technologies. While you can find a detailed breakdown of specific platforms in our curated list of top SMS pumping protection tools, the 2026 landscape is defined by three primary categories of defense.
1. Adaptive CAPTCHA and Behavior Verification
In 2026, the traditional CAPTCHA has evolved from a simple image puzzle into a sophisticated behavioral engine. These tools focus on the “pre-trigger” phase, identifying bots before they can interact with the SMS API.
- 4D Behavior Verification: Next-gen CAPTCHA solutions analyze micro-interactions, such as mouse hover paths, keystroke dynamics, and the physics of touch events. By identifying “inhumanly perfect” patterns, they can distinguish human users from agentic AI scripts.
- Dynamic Friction Logic: If a session is flagged as suspicious, the system deploys an adaptive challenge that requires 3D spatial logic or multi-step reasoning. These tasks are computationally expensive for botnets, destroying the attacker’s ROI while maintaining a seamless experience for verified human users.
2. Silent Network Authentication (SNA)
Following the industry-wide adoption of the GSMA Open Gateway standards, Silent Network Authentication has become a gold standard for companies looking to stop SMS Fraud.
- Carrier-Direct Verification: Instead of sending a visible text code, SNA tools verify the user’s identity through secure, encrypted signaling paths directly with the mobile network. The system confirms the SIM card’s authenticity against the carrier’s real-time subscriber database in the background.
- Zero-Message Infrastructure: Because no traditional SMS message is generated or transmitted, the opportunity for toll fraud is physically removed. This makes SNA an ideal solution for mobile-first environments where cost control is paramount.
3. Persistent Device Fingerprinting
Device fingerprinting has become a critical layer in SMS Toll Fraud Protection, moving beyond IP addresses to track the actual hardware making the request.
- Hardware-Based Attribution: These tools capture deep browser attributes, canvas rendering signatures, and hardware configurations to create a unique ID for every user agent. This allows security systems to recognize when a single device is attempting to trigger hundreds of OTPs, even if it is rotating IPs or using a VPN.
- Velocity Tracking Across Sessions: By maintaining a persistent ID, businesses can implement strict velocity limits on a per-device basis. Tracking device-level behavior is the primary method for enterprises to mitigate “Flash Attacks” that would otherwise bypass traditional IP-based rate limiting.
Case Study: How a Top-tier Social Networking Giant Battles SMS Toll Fraud with GeeTest
Challenge
The platform faced a massive surge in SMS toll fraud while expanding into international markets. Attackers utilized a vast network of residential proxies to rotate IP addresses, bypassing traditional frequency limits. This resulted in tens of thousands of fraudulent SMS messages being triggered to high-cost regions, leading to a significant spike in communication expenses and a high volume of “fake” registrations.
GeeTest Solution
By integrating GeeTest, the platform shifted from passive monitoring to a proactive, multi-layered defense strategy:
- Dynamic Environment Detection: GeeTest’s engine identified emulators and cloud-based automation tools that were disguised as legitimate mobile users.
- Adaptive Friction Strategy: The system deployed 3D spatial logic challenges for high-risk sessions. These challenges are computationally expensive for botnets to solve, effectively destroying the attacker’s ROI.
- Pre-send Intervention: By verifying the user’s intent and legitimacy at the interaction stage, GeeTest prevented the SMS API from being called for fraudulent requests.
The Results
Following the implementation, the platform saw a 90% reduction in abnormal SMS traffic. This not only eliminated tens of thousands of dollars in monthly fraud costs but also improved the overall health of their user database by preventing bot-driven account creation.
Conclusion: Securing Your Communication ROI
As we progress through 2026, SMS Toll Fraud has transitioned from a minor technical risk to a sophisticated financial weapon. The transition from passive monitoring to “Active Immune Protection” is the only sustainable way to stay ahead of AI-powered fraudsters. By integrating behavioral intelligence, persistent device fingerprinting, and carrier-level authentication, businesses can ensure that their communication budget is an investment in real customer growth rather than a payout to a criminal network.