Takeways
CNP fraud is online or remote payment fraud where the physical card is not present. Fraudsters only use stolen card details (number, expiry, CVV) to make purchases.
CNP fraud uses stolen card details without the physical card and has much higher risk. Card Present fraud requires the actual card at a store and is much harder to commit.
It happens in four stages: stealing card data (phishing/breaches), testing cards with small transactions, bypassing security (proxies & spoofing), and finally making high-value purchases or reselling goods.
CNP fraud is rising due to booming e-commerce, abundant stolen card data on the dark web, sophisticated automated attacks, and higher risks in cross-border transactions.
It harms cardholders (frozen accounts, stress), merchants (chargebacks, lost goods, fees), and banks (reimbursement costs, customer loss).
Cardholders should: use digital wallets (Apple Pay/Google Pay), virtual cards, enable transaction alerts, review statements regularly, never share CVV/OTP, and report fraud to the bank immediately.
Merchants should secure payment systems, deploy layered fraud detection (CAPTCHA + device fingerprinting), enable 3D Secure 2.0, monitor chargeback ratios, and avoid unnecessary storage of card data.
Banks can use rule-based systems, risk scoring models, machine learning for real-time detection, and partner with fraud prevention providers that offer guaranteed decisions.
GeeTest helps by blocking card testing bots with adaptive CAPTCHA, identifying repeat fraudsters through device fingerprinting, and stopping fraud rings using a flexible business rules engine.
What is Card Not Present (CNP) Fraud?
Card Not Present (CNP) fraud refers to any fraudulent payment transaction in which the physical payment card is not present at the time of purchase. Instead of using the actual card, fraudsters only need stolen card details such as the card number, expiration date, cardholder name, and CVV code to complete a transaction.
CNP fraud typically occurs in online, mobile, phone, and mail order transactions where merchants cannot verify the physical card, chip, PIN, or cardholder identity in person. As digital payments continue to grow, these transactions have become a primary target for attackers.
Common examples of Card Not Present transactions include:
- Online shopping purchases
- Mobile app payments
- Subscription and recurring billing services
- Travel and hotel bookings
- Food delivery and ride-hailing apps
- Phone or mail order payments
How Is Card Not Present Fraud Different From Card Present Fraud?

Card Not Present (CNP) Fraud and Card Present (CP) Fraud differ mainly in how the fraudulent transaction occurs and the level of risk involved.
Simple Comparison
| Aspect | Card Present (CP) Fraud | Card Not Present (CNP) Fraud |
| Definition | Fraud using the physical card at a store or terminal (swipe, insert, or tap) | Fraud using stolen card details (number, expiry, CVV) without the physical card |
| Typical Scenario | In-person at physical stores or POS terminals | Online shopping, phone orders, app payments |
| Fraud Risk | Much lower (around 0.06% of transaction value) | Significantly higher (around 0.93% or more) |
| Why the Difference? | Physical card + EMV chip + PIN or signature allows better verification | No physical card; merchant relies only on entered information |
| Common Methods | Counterfeit cards, stolen physical cards, skimming | Data breaches, phishing, dark web purchases, card testing |
| Merchant Impact | Lower fees; liability often shifts to issuer with proper tech | Higher processing fees; merchants often bear chargeback losses unless using 3D Secure |
Key Takeaway
- CP Fraud is harder for criminals because the card must be physically presented, and modern chip technology (EMV) makes cloning difficult.
- CNP Fraud is much easier and more common today because anyone with the card number, expiry date, and CVV can make remote purchases — no face-to-face check needed. This is why online fraud has grown rapidly with e-commerce.
How Does Card Not Present Fraud (CNP) Happen?
CNP fraud is rarely a single event; it is a sophisticated, multi-stage process that often involves global criminal networks. Unlike a physical mugging, a CNP attack is digital, scalable, and frequently automated.
The lifecycle of a CNP fraud attack typically follows these four stages:
1. Data Acquisition (The “Harvesting” Phase)
Before a fraudulent transaction can occur, attackers must obtain the card details. They use several high-volume methods:
- Phishing & Smishing: Creating deceptive emails or SMS messages that mimic banks or courier services, tricking users into entering their card details on a fake payment page.
- Magecart / E-skimming: Injecting malicious JavaScript code into the checkout pages of legitimate e-commerce websites to “skim” card data in real-time as customers type it.
- Database Breaches: Direct attacks on ill-secured servers of retailers or service providers to exfiltrate millions of cardholder records at once.
- Dark Web Marketplaces: Purchasing “Fullz” (complete sets of card data) from specialised vendors who sell validated credentials in bulk.
2. Card Testing (The “Validation” Phase)
Once fraudsters have a list of card numbers, they need to know which ones are still active and have available credit.
- Botnets & Automation: Attackers use automated scripts to attempt small, inconspicuous transactions (often $1.00 or less) on sites with weak security, such as charity donation pages or small e-commerce stores.
- Velocity Attacks: Rapidly firing hundreds of payment attempts per minute. If a transaction is approved, the card is marked as “live” and ready for a high-value fraudulent purchase.
3. Circumventing Defences (The “Evasion” Phase)
To avoid triggering the merchant’s fraud filters, sophisticated attackers employ technical tools to mimic legitimate users:
- Proxy & VPN Usage: Routing traffic through residential IP addresses located in the same city as the cardholder to bypass geographic IP filters.
- Device Spoofing: Using specialised software to alter browser fingerprints (User-Agent, screen resolution, time zone) so the connection looks like a standard laptop or mobile phone rather than a server.
- Account Takeover (ATO): Instead of using a new guest account, fraudsters log into an existing customer’s account using stolen passwords, leveraging the “trust” the merchant already has with that user.
4. Execution and Monetisation (The “Payday” Phase)
The final goal is to convert the stolen credit into untraceable assets:
- Digital Goods: Purchasing gift cards, software keys, or in-game currency that can be resold instantly for cryptocurrency.
- Physical Goods & Mules: Buying high-resale items (electronics, designer clothing) and shipping them to “reshipping mules”—individuals hired to receive and forward stolen goods to mask the fraudster’s true location.
- Triangulation Fraud: The fraudster sets up a fake storefront on a popular marketplace, sells an item they don’t own to a real customer, then uses a stolen card to buy that item from a legitimate retailer and ship it to the customer. The fraudster keeps the clean cash from the customer, while the retailer gets hit with a chargeback later.
Why Is Card Not Present Fraud (CNP) Increasing?
Card Not Present fraud continues to rise due to structural trends and exploitable vulnerabilities.
- Digital Payments Are Expanding E-commerce and mobile payments now account for a growing share of transactions. In 2024, global e-commerce sales reached $6.9 trillion, creating more opportunities for CNP fraud. (statista.com)
- Stolen Card Data Is Readily Available Analysis shows over 90% of global card-issuing institutions have had card data exposed in leaks. Dark web markets and automated testing tools make it easy for fraudsters to convert stolen card data into fraudulent transactions. (threathunter.com)
- Attacks Are More Sophisticated Modern fraudsters use AI-generated phishing campaigns, distributed botnets across thousands of IPs, and automated card-testing tools that mimic legitimate behaviour. This allows them to bypass simple fraud detection systems.
- Geographic Differences Increase Risk CNP fraud rates vary widely. For example, Australian-issued cards used domestically see A$0.75 in fraud per A$1,000 spent, but when used with overseas merchants, the rate jumps to A$10.75 per A$1,000—over 14 times higher. (auspaynet.com.au)
These data points show why CNP fraud remains a growing concern for banks, payment providers, and online merchants.
What Are the Impacts of Card Not Present (CNP) Fraud?
1. Consequences for Cardholders
While most modern banking systems offer “Zero Liability” protection, the secondary effects on the individual are significant.
- Financial Disruption & Frozen Funds: Even if the bank eventually reimburses the stolen amount, the victim’s account or credit limit may be frozen during the investigation, leading to missed payments on rent, utilities, or mortgages.
- Credit Score Damage: If a fraudulent transaction goes unnoticed and results in a late payment, it can negatively impact the holder’s credit rating.
- Identity Theft Risk: CNP fraud often means the victim’s sensitive data (Name, Address, CVV) is now for sale on the Dark Web, making them a target for future, more complex identity theft.
- Psychological Stress: The time and effort required to cancel cards, dispute charges, and update automated billing for dozens of services cause significant anxiety and frustration.
2. Consequences for Merchants
In CNP transactions, the “burden of proof” lies with the merchant. Since they cannot physically verify the card or the signature, they are often the hardest hit financially.
- Chargeback Losses: When a cardholder disputes a fraudulent charge, the merchant loses the sale revenue AND the physical inventory already shipped.
- Chargeback Fees: Banks charge merchants a penalty fee for every dispute filed, typically ranging from $15 to $100 per transaction, regardless of who wins the case.
- Increased Operational Costs: Merchants must invest heavily in fraud detection software (like 3D Secure) and manual review teams to vet suspicious orders.
- Risk of “Matching” or Blacklisting: If a merchant’s fraud rate exceeds a certain threshold (usually 1%), payment processors may terminate their account, effectively shutting down their ability to do business online.
3. Consequences for Banks & Financial Institutions
Banks act as the “policemen” of the financial system, and fraud strains their resources and reputation.
- Direct Financial Reimbursements: Issuing banks often absorb the cost of reimbursing the cardholder if the merchant is not found liable.
- High Administrative Costs: Investigating fraud claims, processing paperwork, and issuing/mailing replacement cards involve massive overhead expenses.
- Customer Churn & Loss of Trust: Frequent fraud occurrences—or “False Positives” (blocking a legitimate purchase by mistake)—frustrate customers, leading them to switch to a competitor.
- Regulatory & Compliance Risks: Banks with poor fraud management can face heavy fines from government regulators for failing to uphold Anti-Money Laundering (AML) or security standards.
What Cardholders Can Do?
Cardholders are the first line of defense. While banks ultimately reimburse most fraudulent transactions, prevention saves cardholders from administrative burden, temporary fund freezes, and emotional stress.
| Measure | Description |
| Use digital wallets when possible | Apple Pay and Google Pay use tokenization—transmitting a one-time token instead of your actual card number. Even if a merchant is breached, your real card details are not exposed |
| Use virtual card numbers | Many banks offer virtual card numbers for online shopping with spending limits or expiration dates. Even if stolen, they cannot be used for large transactions |
| Never share CVV or OTP | No legitimate merchant, bank, or customer service representative will ever ask for your CVV code or one-time password by phone, email, or text |
| Enable transaction alerts | Set up SMS or email alerts for all transactions, including small amounts. Early detection of testing transactions allows you to block the card before larger fraudulent purchases occur |
| Review statements regularly | Check transaction history weekly to identify unauthorized charges quickly. Prompt reporting limits further losses |
| Use bank app card controls | Instantly lock/unlock cards, set spending limits, restrict transaction types, or block international usage |
| Report fraud immediately | Contact your bank as soon as you notice unauthorized transactions. Prompt reporting stops further losses and simplifies investigation |
What Merchants Can Do?
Merchants bear significant financial exposure from CNP fraud—chargeback fees, lost goods, and potential loss of payment processing privileges. Unlike cardholders, merchants must actively prevent fraud before it occurs.
| Measure | Description |
| Secure payment infrastructure | Ensure payment gateways are properly secured, enforce strong password policies, and encrypt all customer data. These basic measures close the most common entry points fraudsters exploit |
| Deploy layered fraud detection | Implement CAPTCHA at payment addition, checkout, registration, and login to block automated card testing; use device fingerprinting to identify headless browsers and automation frameworks |
| Enable 3D Secure 2.0 | Shifts liability for fraudulent chargebacks from the merchant to the issuing bank when authentication is successful. Provides risk-based authentication that can exempt low-risk transactions from friction |
| Apply step-up authentication for high-risk transactions | For transactions exceeding thresholds or exhibiting risk indicators, require additional verification—such as OTP, biometrics, or identity document upload |
| Monitor chargeback ratios | Track chargeback rates closely. If ratios approach 0.9% (Visa) or 1.0% (Mastercard), you risk entering monitoring programs with escalating fines or account termination |
| Avoid storing card data unless necessary | If storage is required for recurring billing, use a PCI-compliant tokenization service that stores tokens rather than actual card numbers |
| Evaluate international transaction risk | Cross-border transactions face significantly higher fraud rates. Adjust friction levels based on geographic risk |
What Banks and Financial Institutions Can Do
Banks and payment platforms serve as the infrastructure layer of the payment ecosystem. Their fraud prevention capabilities affect cardholders and merchants alike.
| Approach | Description |
| Rule-based model | Organizations define a set of rules to determine which CNP transactions should be approved, declined, challenged, or sent for review. For example, a merchant may block transactions when the same device attempts multiple cards within a short period or trigger additional verification for high-risk geographies. Modern business rules engines make this approach more flexible by allowing teams to quickly adjust policies as fraud patterns change. |
| Scoring model | A scoring solution evaluates each transaction and generates a risk score based on factors such as device reputation, IP address, purchase history, transaction amount, and user behavior. Merchants then define thresholds to determine whether a transaction should be approved, declined, or manually reviewed. |
| Machine learning-based decisioning | Because CNP fraud is increasingly complex and fast-moving, many organizations use machine learning to analyze millions of signals in real time. Machine learning models can identify suspicious patterns, detect new attack methods, and continuously improve fraud detection accuracy based on emerging behavior. |
| Accountable fraud prevention partner | Some organizations work with fraud prevention partners that provide guaranteed decisions rather than recommendations. In this model, the provider takes responsibility for the cost of approved fraudulent transactions, encouraging highly accurate decisions supported by real-time analytics and machine learning. |
How GeeTest Helps Prevent Card Not Present Fraud
Blocking Card Testing Bots with Adaptive CAPTCHA
One of the earliest stages of CNP fraud is card testing. Fraudsters use bots to submit stolen card numbers to checkout or payment forms in order to determine which cards are still valid.
Traditional CAPTCHA systems are often ineffective because attackers can bypass them using CAPTCHA-solving services or scripted automation. GeeTest uses adaptive CAPTCHA technology that evaluates interaction behavior rather than relying solely on visible challenges.
GeeTest analyzes signals such as:
- Mouse movement patterns
- Click timing and rhythm
- Touchscreen gestures
- Typing speed and sequence
- Navigation behavior before the payment attempt
These behavioral signals make it possible to distinguish between legitimate users and automated scripts, even when the bot attempts to imitate human activity.
When suspicious behavior is detected, GeeTest can trigger a stronger verification challenge or block the request entirely before the fraudster is able to validate stolen card information.
As a result, attackers lose the ability to test large volumes of payment cards, reducing the effectiveness of downstream fraud attempts.
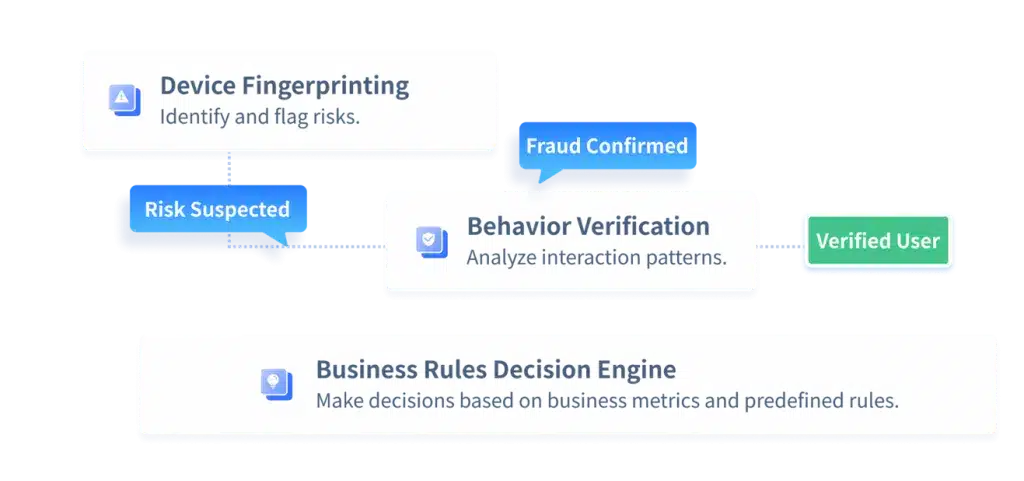
Identifying Repeat Fraudsters with Device Fingerprinting
Fraudsters frequently attempt to hide their identity by changing IP addresses, clearing cookies, switching accounts, or using different browsers. However, the underlying device often remains the same.
GeeTest Device Fingerprinting creates a unique profile for every visitor based on browser, hardware, network, and environmental signals.
This allows GeeTest to detect:
- Multiple stolen cards being tested from the same device
- Large numbers of fake accounts
- Repeat fraud attempts from previously blocked users
- Emulators, virtual machines, and anti-detect browsers
Even when attackers change their visible identity, GeeTest can link activity back to the same device and stop repeat fraud before another transaction is attempted.
Stopping Fraud Rings with Business Rules Engine
Many CNP attacks are not isolated events. Fraudsters often work in organized groups, reusing the same infrastructure across multiple accounts and payment attempts.
GeeTest Business Rules Engine allows merchants to define custom anti-fraud logic based on their own business scenarios.
For example, businesses can create rules such as:
- Block a device that submits more than three different cards within ten minutes
- Trigger verification if multiple accounts use the same device
- Flag high-value purchases made from a newly registered account
- Reject transactions originating from a proxy, VPN, or high-risk region
- Increase risk when the same shipping address is used across multiple unrelated accounts
Because the rules are fully configurable, merchants can adapt quickly as fraud tactics change.
This is especially important for industries with elevated CNP fraud risk, including:
- E-commerce
- Online gaming
- Digital subscriptions
- Travel and ticketing
- Financial services
By combining business rules with device fingerprinting and behavioral analysis, GeeTest helps organizations uncover hidden relationships between accounts, devices, and transactions that would otherwise go unnoticed.
Conclusion
Ultimately, Card Not Present fraud is not caused by a single vulnerability. It is the result of multiple weaknesses across the digital payment journey: stolen card data, automated card testing, fake accounts, device spoofing, and inadequate risk controls. As attackers become faster and more sophisticated, businesses that rely on a single layer of protection will struggle to keep up.
The key to reducing CNP fraud is to build a layered defense strategy that can identify suspicious behavior, recognize repeat attackers, and respond dynamically in real time. Merchants, banks, and payment platforms all play a role, but the most effective protection comes from combining behavioral analysis, device intelligence, and business-specific risk rules into one coordinated system.
CNP fraud may continue to evolve, but organizations that can see the full picture behind every transaction will be far better positioned to stop fraud before it leads to financial loss, chargebacks, and damaged customer trust.