Device spoofing has become the invisible engine driving professional fraud on an industrial scale in 2026.
Imagine a single attacker, armed with nothing more than a standard server, appearing to your security systems as a fleet of ten thousand unique, high-value mobile users. This isn’t just a technical glitch; it is a sophisticated form of environmental manipulation that is currently draining marketing budgets through massive promo abuse and compromising platform integrity via credential stuffing.
As businesses lean more heavily on automated user journeys, the invisibility of these attacks has reached a breaking point. For modern digital enterprises, the inability to distinguish a real physical device from a simulated one is no longer just a security risk—it is their most expensive operational blind spot.
What is device spoofing?
At its core, device spoofing is the act of falsifying or manipulating a device’s unique digital identifiers—such as IP addresses, IMEI numbers, MAC addresses, and hardware serials—to masquerade as a different or entirely new entity. This is achieved through specialized software that sits between the device hardware and the application. When the application requests device info for verification, the spoofing tool intercepts that request and feeds the system a “clean,” randomized, but entirely fake set of parameters.
The ultimate objective of this deception is identity concealment at scale. By mimicking the “fingerprint” of a legitimate, organic user, fraudsters can achieve several high-impact goals:
- Defeat Rate Limits: By pretending to be a “new” user every few seconds, attackers can exploit one-time sign-up bonuses, referral rewards, and limited-time offers indefinitely.
- Bypass Geo-restrictions: Falsifying GPS coordinates and network data allows attackers to access region-locked pricing or circumvent localized security protocols.
- Evade Blacklists: If a specific device identity is flagged for suspicious activity, the attacker simply generates a new, pristine identity in milliseconds, allowing the attack to continue without interruption.
In the 2026 landscape, any identifier that can be read by a standard security script can also be faked. This reality makes the detection of the environment—rather than just the identity—the only viable way to stay ahead of the fraud curve.

How does device spoofing work?
Device spoofing works by utilizing a combination of emulators, hooking frameworks (such as Frida and Xposed), and app cloners to intercept and falsify hardware identifiers. By sitting between the operating system and the application, these tools feed the server a “pristine” set of randomized device parameters, making a single automated server appear as thousands of unique physical devices.
In 2026, the mechanics of a professional spoofing attack have evolved into a four-pillar strategy designed to achieve total environmental mimicry:
- Emulators and Virtual Environments: Fraudsters use high-performance servers to run virtual mobile environments. These emulators can be scripted to mimic thousands of different device models—from budget Androids to the latest iPhones—at a massive scale without owning a single physical handset.
- Hooking Frameworks (The “Brain”): This is the core of modern deception. Tools like Frida or Xposed allow attackers to inject custom code into an app’s process. When your app asks the system for a device’s IMEI or serial number, the framework intercepts the request and provides a fake, randomized value before the data ever leaves the device.
- App Cloning and Sandboxing: Attackers use specialized software to create isolated “sandboxes” on a single device. This allows them to run hundreds of instances of the same application simultaneously, with each instance maintaining its own isolated cookies, cache, and spoofed identity.
- Residential Proxy Pairing: To complete the illusion of legitimacy, spoofed devices are paired with residential proxies. By routing traffic through genuine home Wi-Fi networks in specific cities, attackers ensure their network signature looks like a real local customer rather than a data center bot.
Why is device spoofing a threat to your business?
Device spoofing is a multi-billion-dollar threat because it enables mass-scale fraud that bypasses identity-based security, with suspected digital account creation fraud peaking at 8.3% of all global attempts in 2025. By allowing a single attacker to masquerade as thousands of unique, trusted devices, spoofing leads to devastating financial losses. According to the TransUnion H1 2026 Fraud Trends Report, the suspected digital fraud rate for account takeover (ATO) skyrocketed by 37% year-over-year as attackers leveraged spoofed environments to mimic legitimate users.
The impact of this “invisible” threat manifests in three critical areas:
- Marketing & Promo Abuse: Fraudsters use spoofed devices to “farm” rewards. New research from Juniper Research (2026) indicates that e-commerce fraud is projected to rise from $56 billion in 2025 to over $131 billion by 2030, heavily driven by “bad actors blending in” through the misuse of promotions.
- Ad Fraud & Wasted Spend: Digital ad fraud is projected to exceed $100 billion in 2026. According to Modern Diplomacy (April 2026), spoofing allows bots to generate fake clicks and installs that appear to come from premium mobile devices, effectively draining marketing ROI.
- AI-Driven Scale: The threat is accelerating; HUMAN Security’s 2026 Benchmark Report reveals that AI-driven automation is growing 8x faster than human traffic, making manual detection impossible.
Why do traditional defenses fail against device spoofing in 2026?
Traditional defenses fail because they rely on static identifiers and client-side signals that are now easily intercepted or simulated, with standard fraud detection techniques now detecting less than 40% of sophisticated bot traffic. As fraudsters adopt “total environmental mimicry,” simple IP blacklisting and basic device fingerprinting can no longer distinguish between a high-value human customer and a malicious automated script.
The obsolescence of legacy security layers is driven by several factors:
- The Ineffectiveness of Static Identifiers: Any identifier that can be read (like IMEI, MAC address, or cookies) can be faked. 2026 industry analysis shows that 50% of sophisticated fraudsters now use residential proxies and mobile botnets to rotate IP addresses, rendering IP filtering alone insufficient.
- Explosive Growth in Agentic Traffic: According to LexisNexis Risk Solutions (March 2026), “agentic” traffic—automated bots posing as humans—rose 450% in 2025, specifically targeting logins and account creation at e-commerce and gaming sites.
- The Precision of “Anti-Detect” Technology: Fraudsters now use specialized browsers and frameworks that adapt their “behavioral DNA” in real-time. This creates a reality where the line between legitimate automation and fraud has narrowed to half a percentage point, making static rules and basic detection systems obsolete.
How can you stop device spoofing in 2026?

To stop device spoofing in 2026, businesses must shift from static identification to multi-layered, dynamic risk analysis that focuses on “environmental integrity” rather than just the device ID. Instead of relying on a single identifier like an IP or MAC address, the solution lies in cross-referencing hundreds of hardware, software, and behavioral signals in real-time.
A comprehensive defense strategy against sophisticated spoofing now requires three key technical pillars:
- Deep Device Fingerprinting (Device DNA): Rather than reading simple IDs, modern solutions collect “entropy” from a device’s core hardware. This includes GPU rendering patterns (WebGL), battery health characteristics, and system font lists. These attributes form a “Device DNA” that is nearly impossible for a simulator to replicate perfectly across thousands of fake accounts.
- Real-Time Environment Risk Analysis: Security systems must be able to detect the “tools of the trade” while they are in use. This means identifying the presence of hooking frameworks (like Frida or Xposed), detecting if an app is running in an emulator, or flagging “virtualized” operating systems that are common in professional bot farms.
- Behavioral Intelligence Integration: Because spoofed devices are often controlled by scripts, analyzing how the device is used—such as mouse movement fluidity, touch gesture pressure, and navigation speed—provides a critical second layer of verification. If the “device” looks like an iPhone but the “user” moves with the mechanical precision of a bot, the request can be instantly flagged.
What is the best solution for device spoofing prevention?
The best solution for preventing device spoofing in 2026 is an AI-driven identification engine that moves beyond simple detection to provide a comprehensive risk score and actionable intelligence. For businesses seeking to eliminate fraud while maintaining growth, GeeTest Device Fingerprinting offers a decisive advantage through four core pillars:
- Triple-Dimensional Review for Unmatched Accuracy: Unlike legacy systems, GeeTest evaluates device historical data, attribution, and real-time risk factors simultaneously. This ensures that even if a fraudster clears their cache or uses a virtualised environment, the system maintains a persistent and accurate identity.
- Seamless User Experience (UX): Security shouldn’t come at the cost of conversion. GeeTest performs deep-level environmental checks in the background, remaining “invisible” to legitimate customers while ensuring zero friction in the user journey.
- Actionable Risk Tagging: Every device is assigned specific risk tags—such as emulator detection, proxy usage, or rooting. This provides your team with a clear, predictable, and granular view of traffic to drive precise policy management.
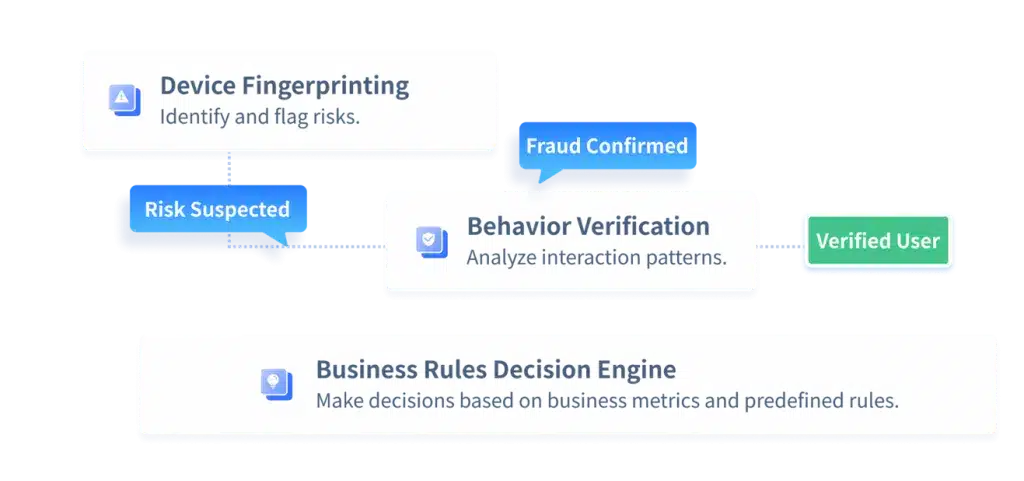
- Modular “Defense-in-Depth” Integration: GeeTest allows you to combine device identification with Behavior Verification and the Business Rules Decision Engine. This synergy introduces Dynamic Defense Logic, forcing suspicious devices to solve real-time challenges while linking technical risks directly to your specific business logic (e.g., payment thresholds or registration limits).
By integrating these modules, you create a unified, intelligent system that protects every stage of the user lifecycle—from initial ping to final transaction. This multi-layered approach ensures that as spoofing tactics evolve, your defense remains one step ahead by making it economically and technically unfeasible for fraudsters to maintain their deception.
Conclusion
As we move through 2026, the battle against device spoofing is no longer about “who” is visiting your site, but “what” environment they are using to get there. The techniques used by attackers are in a state of constant evolution; for instance, the rise of Bare Metal Cloud Phones represents a new frontier where fraudsters utilize genuine, high-performance hardware at scale to bypass traditional emulator detection.
In this escalating arms race, transitioning to a multi-layered, AI-powered strategy—integrating device fingerprinting, behavioral verification, and business-level decisioning—is the only way to ensure your digital doors remain open to customers and closed to fraudsters.




